Week two of Cybersecurity Awareness Month focuses on “Fight the Phish.” If you’ve gotten by no means obtained a phishing e-mail, you in all probability don’t have an e-mail deal with. They are usually far more frequent than precise enterprise correspondence. Beyond that, you possibly can say that there are two sorts of folks on the earth – those who have clicked on a phishing e-mail, and those that will achieve this sooner or later.
Phishing stays one of many best and commonest methods to hack a pc, get private knowledge, or unfold malware. Securing a website and sending hundreds of faux emails price little, and even when one particular person in 100 opens one or clicks on a hyperlink, the attacker has entry to do any of the above. According to the Verizon 2021 Data Breach Investigation Report, Phishing is among the prime breach actions. 36% of all breaches in 2020 have been associated to phishing, an 11% improve from 2019.
It’s particularly troublesome when folks use their work e-mail for private functions. That approach private emails get commingled with enterprise correspondence. And as a consequence of their nature, private emails usually tend to include spam and different phishing hyperlinks.
Keep Up-to-date with Phishing Attack Trends
It’s essential to know what strategies attackers are leveraging so you possibly can warn your customers and replace your detection instruments. The FBI maintains a web site with of frequent spoofing and phishing assaults. There yow will discover assets and up to date information. And details about recognized phishing assaults might be discovered on the Anti-Phishing Working Group web site. The group publishes a quarterly Phishing Activity Trends Report. Here is the report for 2nd quarter 2021.
Over the previous few years, Gurucul has noticed the next new developments in phishing assaults:
Phishing e-mail adopted by Phone Call: A brand new development being noticed is a phishing marketing campaign adopted up by an precise cellphone name. On the fraudulent name, the caller would usually recommend that the e-mail recipient open the e-mail. Given the immediacy and strain of one other particular person asking them to click on on the phishing e-mail in real-time, fairly often the sufferer would click on on the hyperlink and because of this, the pernicious payload will get launched on the community.
Business e-mail compromise: Business Email Compromise (BEC) can also be frequent wherein an attacker obtains entry to a enterprise e-mail account and imitates the proprietor’s id, with the intention to defraud the corporate and its staff, prospects or companions.
Credential Theft: Credential theft by way of social engineering and phishing continues to be a excessive precedence for cybercriminals. With hijacked e-mail, community, and software login data, menace actors can additional infiltrate networks and methods to execute BEC techniques, set up malware and ransomware, steal personally identifiable data, and plunder mental property and confidential data
Educate Your Users
So particularly inside a company, how can we struggle the phish? How can we assist customers navigate via their day on the pc safely?
The first step is schooling. We can break that down into a number of elements. First, it entails getting customers to consider cybersecurity every time they’re on-line. A heightened consciousness of the dangers is an important start line in establishing a basis for safety.
Second, customers must learn about energetic phishing makes an attempt. Often they appear to return from authentic sources – companions, banks, pharmacies, or shops, for instance. There are sometimes telltale indicators, equivalent to misspellings and weird hyperlinks, that point out a specific e-mail isn’t authentic. Users must be skilled in figuring out these indicators.
Phishing may also be accompanied by social engineering strategies, equivalent to cellphone calls, visits by colleagues, social media notifications, and follow-up emails. Users usually tend to click on on phishing hyperlinks if they’re accompanied by a customized follow-up.
Beyond that, if there are any publicly recognized and prevalent phishing makes an attempt, organizations must let their customers learn about them. Phishing makes an attempt have a tendency to return in acquainted waves, and the extra data customers have, the higher outfitted they’re to deal with them.
Of course, this additionally comes with an obligation to inform customers what to do in the event that they encounter such makes an attempt. Education not solely refers to data on learn how to determine phishing makes an attempt, but in addition what to do about them. In many instances, that reply is to report them to IT employees or cybersecurity employees, however customers want these messages strengthened regularly.
Detect Phishing Attacks Automatically with Machine Learning
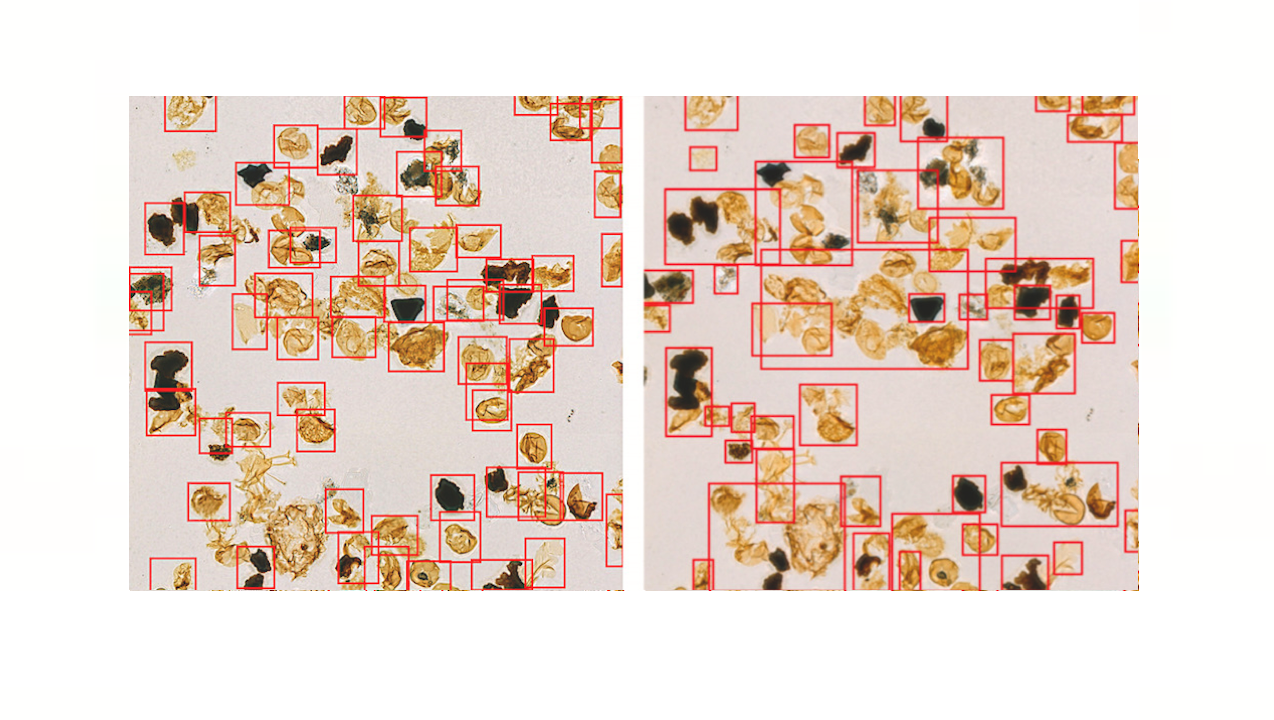
The second factor that enterprises ought to do is constantly monitor for doable assaults. While few organizations have the inclination or assets to learn all incoming e-mail, something outdoors of the abnormal can and must be flagged for additional investigation. This must be a largely automated course of, and Gurucul’s Unified Security and Risk Analytics platform determines the diploma of danger with emails in actual time.
Gurucul offers a variety of pre-packaged supervised machine studying (ML) fashions specifically skilled to detect particular sorts of phishing assaults. These fashions aren’t signature-based however somewhat “skilled” on real-world menace knowledge units to detect and seize varied recognized phishing assaults.
Among the info that prepare these phishing ML fashions are:
Unusual character sequences based mostly on textual content mining
Pretrained detection on trusted topic traces
Unusual sender e-mail domains
Inbound e-mail from related senders to massive numbers of inside customers
While emails might be troublesome to watch, and phishing typically makes use of a number of e-mail addresses, domains, and names, it’s doable for algorithms to determine emails and different knowledge that doesn’t match into the traditional discourse for particular person customers.
Below are particulars on the telemetry and obtainable Gurucul fashions for detecting varied phishing assaults out-of-the-box:
Telemetry
Perpetrator
Victim
Tactic
Data Sources
High Level Model Use Cases
Email
External Bad Actor
Internal Employee
Phishing, Spear- Phishing,
Email, Proxy, Windows Security
Text and Symantec analytics
Inconsistent e-mail deal with, hyperlinks, and domains
Detection of menace and weird urgency
Suspicious topic/attachment
Unusual course of
Unseen area or person
Domain generated algorithm
Unusual / Inconsistent request
File Format Exploits/URLs
Phone / VOIP
External Bad Actor
Internal Employee
Reconnaissance, Trusted Relationship
VOIP logs
Unseen location / supply / protocol
Unusual / extreme name period, frequency
Brute Force / Unusual in-bound visitors
Social Media
External Bad Actor
Internal Employee
Phishing
Proxy, DLP
Traffic sample
Behavior Manipulation
Data switch off of the community
Abnormal printing conduct
AllTraffic
InternalBad Actor
Internal Employee
Insider Threat Use Cases
Multiple
Robotic sample
HR Stressers – Financial, private, addictive, disgruntled / departing / new rent
Data exfiltration
Wanderer conduct
Employee Snooping
Have a Mitigation Strategy
Despite finest efforts, it’s doubtless that somebody will click on on one thing that brings phishing house to roost. Enterprises do their finest to teach and detect potential assaults, nevertheless it solely takes one to slide via. There must be a plan to execute when this occurs, together with figuring out all affected customers and speaking the mitigation plan.
Internal customers are the important thing right here. They are on the entrance traces of phishing assaults, and must resolve which emails are authentic, and which include malware. To achieve this, they want common coaching and knowledge on what to search for, and the way to answer potential assaults. In explicit, customers must develop a “no confidence” perspective towards emails with uncommon topic traces or unknown senders, and report these emails to the consultants that may look additional into them.
And by all means, except customers are sure of the sender and content material, they need to all the time observe finest practices for thwarting phishing assaults: don’t open emails from folks you don’t know or aren’t anticipating communications from, don’t click on on hyperlinks in such emails, and don’t open any attachments.
As all the time, one of the best offense is an efficient protection. Gurucul will help. Contact us for extra data on our Unified Security and Risk Analytics platform.
The publish Fight Phishing Attacks with Machine Learning Powered Security Analytics appeared first on Gurucul.
*** This is a Security Bloggers Network syndicated weblog from Blog – Gurucul authored by Peter Varhol. Read the unique publish at: https://gurucul.com/blog/fight-phishing-attacks-with-machine-learning-powered-security-analytics