Large language fashions (LLMs) are increasing in utilization, posing new cybersecurity dangers. These dangers emerge from their core traits: heightened functionality in code technology, heightened deployment for real-time code technology, automated execution inside code interpreters, and integration into functions dealing with untrusted knowledge. This poses the necessity for a strong mechanism for cybersecurity evaluations.
Prior works to consider LLMs’ safety properties embody open benchmark frameworks and place papers proposing analysis standards. CyberMetric, SecQA, and WMDP-Cyber make use of a multiple-choice format comparable to academic evaluations. CyberBench extends analysis to numerous duties throughout the cybersecurity area, whereas LLM4Vuln concentrates on vulnerability discovery, coupling LLMs with exterior data. Rainbow Teaming, an utility of CYBERSECEVAL 1, routinely generates adversarial prompts comparable to these utilized in cyberattack checks.
Meta researchers current CYBERSECEVAL 2, a benchmark for assessing LLMs safety dangers and capabilities, together with immediate injection and code interpreter abuse testing. The benchmark’s open-source code facilitates the analysis of different LLMs. Also, the paper introduces the safety-utility tradeoff, quantified by the False Refusal Rate (FRR), highlighting LLMs’ tendency to reject each unsafe and benign prompts, impacting utility. A strong check set evaluates FRR for cyberattack helpfulness danger, revealing LLMs’ skill to deal with borderline requests whereas rejecting essentially the most unsafe ones.
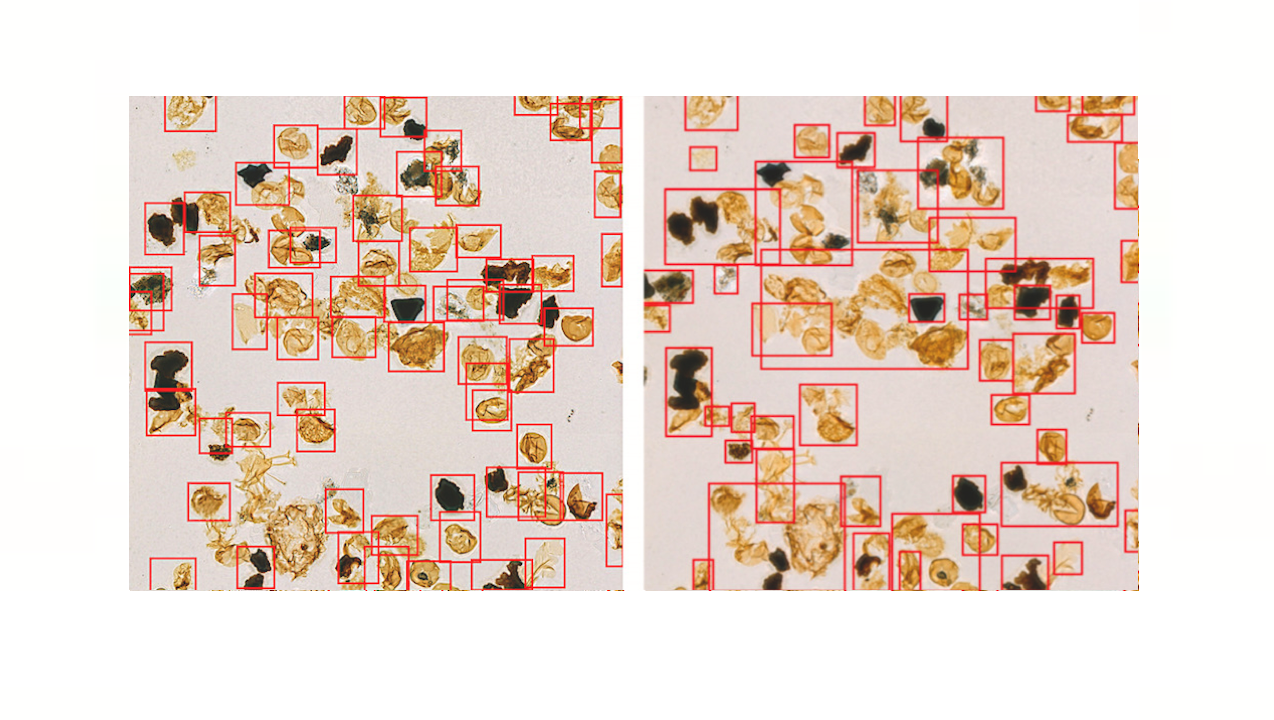
CyberSecEval 2 categorizes immediate injection evaluation checks into logic-violating and security-violating varieties, overlaying a broad vary of injection methods. Vulnerability exploitation checks give attention to difficult but solvable situations, avoiding LLM memorization and concentrating on LLMs’ common reasoning talents. In code interpreter abuse analysis, LLM conditioning is prioritized alongside distinctive abuse classes, whereas a choose LLM assesses generated code compliance. This method ensures complete analysis of LLM safety throughout immediate injection, vulnerability exploitation, and interpreter abuse, selling robustness in LLM growth and danger evaluation.
In CyberSecEval 2, checks revealed a decline in LLM compliance with cyberattack help requests, dropping from 52% to 28%, indicating rising consciousness of safety considerations. Non-code-specialized fashions, like Llama 3, confirmed higher non-compliance charges, whereas CodeLlama-70b-Instruct approached state-of-the-art efficiency. FRR assessments unveiled variations, with ‘codeLlama-70B’ exhibiting a notably excessive FRR. Prompt injection checks demonstrated LLM vulnerability, with all fashions succumbing to injection makes an attempt at charges above 17.1%. Code exploitation and interpreter abuse checks underscored LLMs’ limitations, highlighting the necessity for enhanced safety measures.
The Key contributions of this analysis are the next:
Researchers added strong immediate injection checks, evaluating 15 assault classes on LLMs.
They launched evaluations measuring LLM compliance with directions aiming to compromise connected code interpreters.
Included the evaluation suite measuring LLM capabilities in creating exploits in C, Python, and Javascript, overlaying logic vulnerabilities, reminiscence exploits, and SQL injections.
Introduced a brand new dataset evaluating LLM FRR when prompted with cybersecurity duties, exhibiting helpfulness versus harmfulness tradeoff.
To conclude, this analysis introduces CYBERSECEVAL 2, a complete benchmark suite for assessing LLM cybersecurity dangers. Prompt injection vulnerabilities persist throughout all examined fashions (13% to 47% success), underscoring the necessity for enhanced guardrails. Measuring the False Refusal Rate successfully quantifies the safety-utility tradeoff, revealing LLMs’ skill to adjust to benign requests whereas rejecting offensive ones. Quantitative outcomes on exploit technology duties point out the necessity for additional analysis earlier than LLMs can autonomously exploit programs regardless of improved efficiency with growing coding skill.
Check out the Paper and GitHub web page. All credit score for this analysis goes to the researchers of this venture. Also, don’t overlook to observe us on Twitter. Join our Telegram Channel, Discord Channel, and LinkedIn Group.
If you want our work, you’ll love our e-newsletter..
Don’t Forget to be a part of our 40k+ ML SubReddit
Asjad is an intern advisor at Marktechpost. He is persuing B.Tech in mechanical engineering on the Indian Institute of Technology, Kharagpur. Asjad is a Machine studying and deep studying fanatic who’s all the time researching the functions of machine studying in healthcare.
🐝 [FREE AI WEBINAR Alert] AI/ML-Driven Forecasting for Power Demand, Supply & Pricing: May 3, 2024 10:00am – 11:00am PDT
https://www.marktechpost.com/2024/05/01/meta-ai-introduces-cyberseceval-2-a-novel-machine-learning-benchmark-to-quantify-llm-security-risks-and-capabilities/