In latest years, organizations have moved shortly to combine new AI know-how into their enterprise processes, from fundamental machine learning models to generative AI instruments like ChatGPT. Despite providing quite a few enterprise benefits, nevertheless, the mixing of AI expands organizations’ assault surfaces.
Threat actors are continuously searching for methods to infiltrate goal IT environments, and AI-powered instruments can change into one other entry level to use. AI safety methods are important to safeguard firm information from unauthorized entry.
MLSecOps is a framework that brings collectively operational machine learning (ML) with safety considerations, aiming to mitigate the dangers that AI/ML models can convey to a corporation. MLSecOps focuses on securing the information used to develop and prepare ML models, mitigating adversarial assaults in opposition to these models, and making certain that developed models comply with regulatory compliance frameworks.
The dangers of AI adoption
ML models may help organizations improve effectivity by automating repetitive duties, bettering customer support, lowering operational prices and sustaining aggressive benefits.
But ML adoption additionally introduces dangers at totally different factors, together with in the course of the growth and deployment phases, particularly when utilizing open supply giant language models (LLMs). The following are among the many most important dangers:
Bias. AI instruments may give biased outcomes based mostly on the information they skilled on.
Privacy violations. AI instruments are sometimes skilled on huge quantities of knowledge, and typically it’s unclear whether or not the house owners of that information gave consent for its use in AI coaching. For instance, an AI coding software may be skilled on code snippets from software program initiatives in GitHub repositories that include secrets and techniques, corresponding to account credentials.
Malware. Developers may inject malicious code into their LLM to make it behave maliciously or to supply inaccurate outcomes. For instance, a compromised LLM might be utilized in a malware scanner to acknowledge particular malware code as benign.
Insecure plugins. Many LLMs permit using plugins to obtain freeform textual content. Maliciously crafted enter textual content may execute distant malicious code, resulting in a privilege escalation assault.
Supply chain assaults. Many distributors use pretrained models from third-party suppliers for his or her AI instruments. These models may include backdoors or be designed with safety flaws that facilitate unauthorized entry to the software in a corporation’s provide chain.
IT infrastructure danger. AI instruments are in the end software program packages that want computing infrastructure to run on, corresponding to servers for internet hosting and networking gadgets to facilitate entry to the mannequin. If menace actors attain the underlying {hardware} the place the ML mannequin is deployed, they will conduct varied assaults in opposition to it, corresponding to mannequin extraction, or disrupt the service by focusing on it with denial of service assaults to have an effect on the ML mannequin’s efficiency or availability.
MLSecOps and its main advantages
The time period MLOps refers back to the strategy of operationalizing ML models in manufacturing. It includes a number of phases:
Select the ML mannequin structure and select the coaching information units.
Clean and preprocess the coaching information for the ML mannequin.
Train the mannequin and consider the mannequin’s efficiency on metrics corresponding to accuracy and precision.
Deploy the mannequin into the manufacturing surroundings.
Monitor the mannequin’s ongoing efficiency after deployment to make sure it really works nicely in varied real-world circumstances.
MLSecOps, subsequently, is a pure extension of MLOps. Similar to how DevOps developed into DevSecOps by integrating safety practices into the software program growth lifecycle, MLSecOps ensures that ML models are developed, examined, deployed and monitored utilizing safety finest practices.
MLSecOps integrates safety practices all through the ML mannequin growth course of. This integration ensures the safety of ML models in two areas:
The safety of the information used to coach and take a look at the ML mannequin.
The safety of the IT infrastructure used to host and run the ML models.
5 safety pillars of MLSecOps
MLSecOps particularly focuses on the safety points associated to ML techniques. The following are the 5 primary safety pillars that MLSecOps addresses.
1. Supply chain vulnerability
Like different software program instruments, ML techniques continuously use parts and companies from varied third-party suppliers, creating a posh provide chain. A safety vulnerability in any element throughout the ML system provide chain may permit menace actors to infiltrate it and conduct varied malicious actions.
Typical provide chain parts for an ML system embody the next:
Software and {hardware} parts from exterior suppliers.
Use of an exterior supplier, corresponding to a cloud supplier, to host the ML mannequin.
Use of a service from an exterior supplier to supply the communication infrastructure between the ML system — for instance, hosted on the cloud — and its customers, who’re unfold throughout totally different areas.
The U.S. was the pioneer in addressing the safety points associated to the software program provide chain. In 2021, the Biden administration issued Executive Order 14028, which requires all organizations in each private and non-private sectors to handle safety vulnerabilities of their provide chain.
2. Model provenance
Model provenance is anxious with monitoring an ML system’s historical past by growth, deployment, coaching, testing, and monitoring and utilization. Model provenance helps safety auditors determine who made particular adjustments to the mannequin, what these adjustments had been and after they occurred.
Some parts included within the mannequin provenance of an ML system embody the next:
Data sources used to coach the ML mannequin.
Changes made to ML algorithms.
Information concerning retrained models, together with when it was retrained, any new coaching information and that information’s sources.
ML mannequin use over time.
Model provenance is important to conform with the assorted information safety compliance laws, such because the GDPR within the European Union, HIPAA within the United States and industry-specific laws such because the Payment Card Industry Data Security Standard.
3. Governance, danger and compliance
Governance, danger and compliance (GRC) frameworks are used inside organizations to satisfy authorities and industry-enforced laws. For ML techniques, GRC spans a number of parts of MLSecOps, with the first purpose of making certain that organizations are utilizing AI instruments responsibly and ethically. As extra organizations construct AI-powered instruments that depend on ML models to carry out enterprise capabilities, there’s a rising want for strong GRC frameworks within the use and growth of ML techniques.
For occasion, when creating an ML system, organizations ought to preserve an inventory of all parts utilized in growth, together with information units, algorithms and frameworks. This record is now often known as the machine learning invoice of supplies (MLBoM). Similar to a software program invoice of supplies for software program growth initiatives, MLBoMs doc all parts and companies used to create AI instruments and their underlying ML models.
4. Trusted AI
Trusted AI offers with the moral points of utilizing AI instruments for various use instances as extra organizations depend on AI instruments to carry out job capabilities, together with vital ones. There is an rising want to make sure that AI instruments and their underlying ML models are giving moral responses and usually are not biased in any approach in direction of traits like race, gender, age, faith, ethics or nationality.
One methodology to examine the equity of AI instruments is to request that they clarify their solutions. For occasion, if a consumer asks a generative AI software to suggest the very best nation to go to in summer season, the mannequin ought to present a justification for its reply. This rationalization helps people perceive what elements influenced the AI software’s resolution.
5. Adversarial machine learning
Adversarial machine learning is anxious with finding out how menace actors can exploit ML techniques in varied methods to conduct malicious actions. There are 4 main kinds of adversarial ML:
Poisoning. Threat actors inject malicious information into ML coaching information units, inflicting them to supply incorrect solutions.
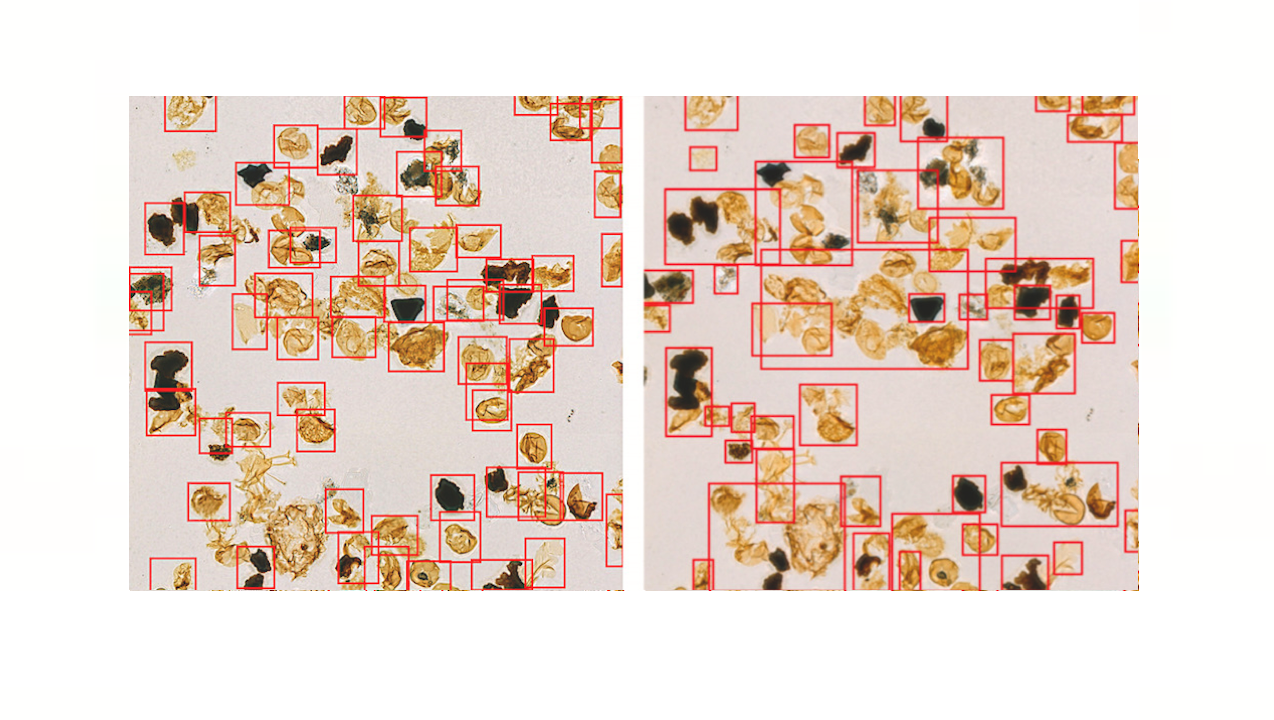
Evasion. This assault happens after the ML mannequin has completed coaching. It includes sending specifically crafted prompts to the ML system to elicit incorrect responses. An instance is altering a photograph of a canine barely to trick the ML system into misidentifying it as a constructing.
Inference. Threat actors attempt to reverse engineer the ML mannequin to disclose what information was used to coach the mannequin, which may include extremely delicate info.
Extraction. In this assault, menace actors attempt to extract or replicate both your complete ML mannequin or simply the information used to coach it.
MLSecOps finest practices
ML growth groups can use the MLSecOps methodology effectively to mitigate cyberattacks when creating ML models. The following are some MLSecOps finest practices:
Identify threats related with ML. Identify potential assault vectors associated to ML growth. For occasion, there are particular safety vulnerabilities that pertain to ML growth, corresponding to information poisoning, mannequin extraction and adversarial pattern assaults.
Secure mannequin information. If the information used to coach the mannequin incorporates delicate info, corresponding to prospects’ personally identifiable info, that information ought to be appropriately masked by encryption or different means.
Use sandboxing know-how. The growth surroundings of the ML models ought to be remoted from the manufacturing surroundings. This ensures attackers can not entry ML models in the course of the growth part, wherein the mannequin is beneath testing and may be inadequately protected.
Scan for malware. All software program parts used to create the ML mannequin, particularly open supply ones, ought to be scanned for malware and different safety vulnerabilities. Components coming from third-party suppliers ought to be scanned completely to make sure they’re free from safety holes.
Perform dynamic testing. Dynamic testing includes supplying malicious prompts to the ML mannequin throughout testing to make sure it may well deal with them. This is important for LLMs which are uncovered to the web.
Nihad A. Hassan is an impartial cybersecurity advisor, an professional in digital forensics and cyber open supply intelligence, and a blogger and guide writer. Hassan has been actively researching varied areas of knowledge safety for greater than 15 years and has developed quite a few cybersecurity training programs and technical guides.
https://www.techtarget.com/searchitoperations/tip/Secure-your-machine-learning-models-with-these-MLSecOps-tips