To develop a shared machine studying mannequin, federated studying algorithms have been created to take benefit of the cooperative utilization of dispersed information. Systemic privateness points might be decreased since taking part clients do not share coaching information. However, latest analysis demonstrates that by reconstructing delicate information from gradients or mannequin states which might be shared throughout the federated coaching, the privateness of taking part shoppers may be jeopardized. Iterative gradient inversion assaults allow the most adaptable reconstruction methods. These strategies improve randomly initialized dummy photos to produce dummy gradients which might be similar to the gradient of the focused shopper.
For instance, they’re rising the batch dimension or the quantity of native coaching iterations and altering the enter information to embody perturbation or enter encryption. Apart from this, altering the exchanged gradient info to embody noise, compression, pruning, or making use of specifically created architectural options or modules are all examples of protection methods towards such assaults. However, most defensive programs drive a trade-off between mannequin performance and privateness.
Dropout is a regularisation methodology utilized in deep neural networks to scale back overfitting. While dropout can enhance neural community efficiency, present research point out that it might protect shared gradients from gradient leaking. These discoveries served as our inspiration, and the researchers used recurrent gradient inversion assaults to reveal that the stochasticity generated by dropout does protect shared gradients towards gradient leaking. However, in accordance to our argument, this protection is solely seen as a result of the attacker lacks entry to the explicit implementation of the stochastic shopper mannequin used for coaching.
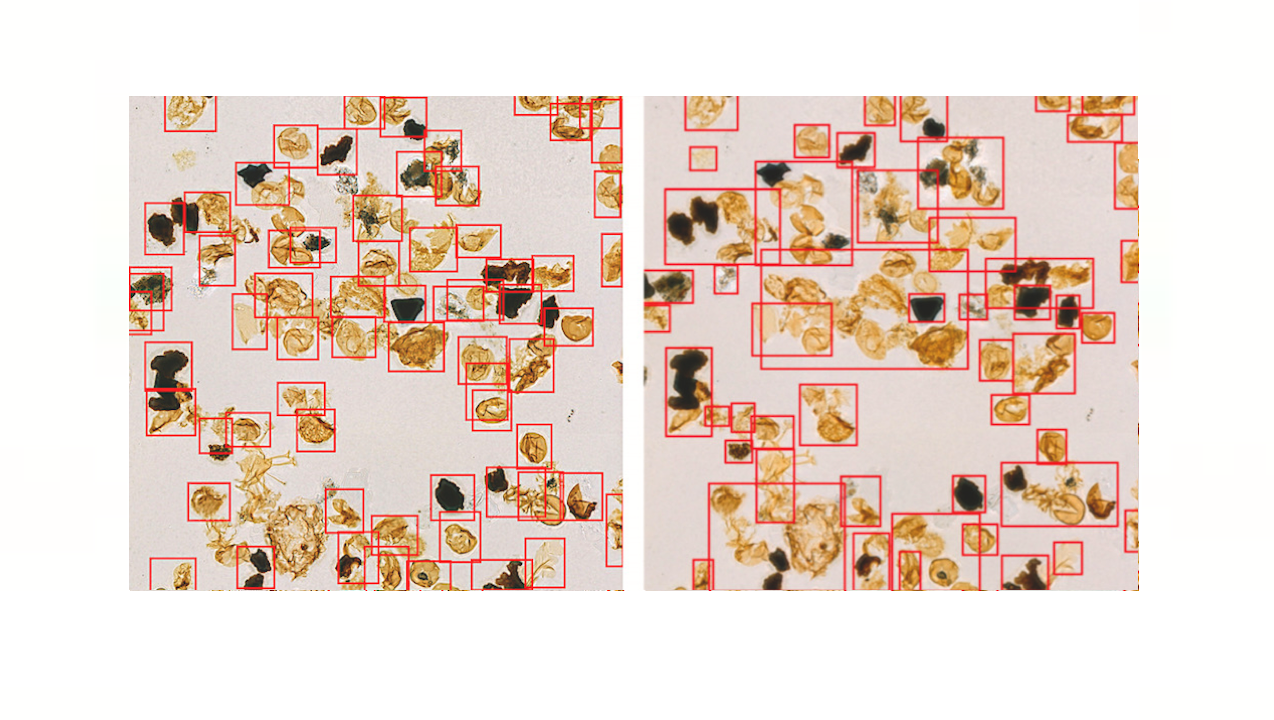
Furthermore, the researchers contend that an attacker can use the shared gradient info to sufficiently simulate this explicit instantiation of the shopper mannequin. They develop a distinctive Dropout Inversion Attack (DIA) that optimizes for shopper enter and the dropout masks used throughout native coaching to expose the weak spot of dropout-protected fashions. The following abstract of our contributions: • Using a methodical strategy, they reveal how dropout throughout neural community coaching seems to cease repetitive gradient inversion assaults from leaking gradient info. •, Unlike different assaults, the distinctive strategy they develop appropriately reconstructs shopper coaching information from dropout-protected shared gradients.
Be conscious that every other iterative gradient inversion approach could also be prolonged utilizing the components of our advised methodology. • The researchers conduct a thorough, systematic analysis of their assault on three more and more sophisticated picture classification datasets, two CNN-based (LeNet, ResNet) and dense connection-based (Multi-Layer Perceptron, Vision Transformer) mannequin architectures (MNIST, CIFAR-10, ImageNet).
There is a GitHub repository shred by the showing authors in the reference part named Inverting Gradients. How simple its to break federated programs. The code implementation on the repository has the approach to regenerate information from gradient info.
This Article is written as a analysis abstract article by Marktechpost Staff based mostly on the analysis paper ‘Dropout is NOT All You Need to Prevent Gradient Leakage’. All Credit For This Research Goes To Researchers on This Project. Check out the paper and github hyperlink.
Please Don’t Forget To Join Our ML Subreddit
Content Writing Consultant Intern at Marktechpost.
https://www.marktechpost.com/2022/09/05/in-a-latest-machine-learning-research-researchers-question-the-ease-of-leaking-data-from-inverting-gradient-highlighting-dropout-is-not-enough-to-prevent-leakage/