Machine Learning (ML) and, in specific, Deep Learning is drastically altering the way in which we conduct enterprise as now information could be utilized to information enterprise methods to create new worth, analyze clients and predict their habits, and even present medical prognosis and care. We might imagine that information is in danger when these algorithms suggest and direct our purchases on social media or monitor our doorways, aged, and kids, however that’s solely the tip of the iceberg. Data is used to make banking selections, detect fraudulent transactions, and determine insurance coverage charges. In all these circumstances, the info is embroiled with delicate data relating to enterprises and even people and the advantages are entangled with information dangers.
One of essentially the most essential challenges that firms are going through right now is knowing the right way to deal with and defend their very own information whereas utilizing it to enhance their companies via ML options. The information contains clients’ private data in addition to enterprise information, corresponding to information relating to the gross sales of an organization itself. Clearly, it’s important for a corporation to accurately deal with and defend such information since its publicity can be an enormous vulnerability.
Source: (*3*)
Specifically, it’s price mentioning three important enterprise challenges about information safety:
First, firms must learn the way to supply protected entry to massive datasets for his or her scientists to coach ML fashions that present novel enterprise worth. Second, as a part of their digital transformation efforts, many firms are likely to migrate their ML processes (coaching and deployment) to cloud platforms the place they are often extra effectively dealt with at a large-scale. However, exposing the info these ML processes eat to the cloud platform comes with its personal related information dangers.Third, organizations that wish to benefit from third-party ML-backed companies should at the moment be prepared to relinquish possession of their delicate information to the supplier of these companies.
To handle these challenges and be broadly relevant, two important objectives should be met:
Separate plain-text delicate information from the machine studying course of and the platform throughout each the coaching and the inference levels of the ML lifecycle;Fulfill this goal with out considerably impacting the efficiency of the ML mannequin and the platform on which it’s skilled and deployed.
In current years, ML researchers have proposed totally different strategies to guard the info that might be utilized by ML fashions. However, none of those options satisfies each the above-mentioned objectives. Most importantly, Protopia AI’s Stained Glass Transform™ resolution is the one resolution available on the market that provides a layer of information safety throughout inference with out requiring specialised {hardware} or incurring important efficiency overheads.
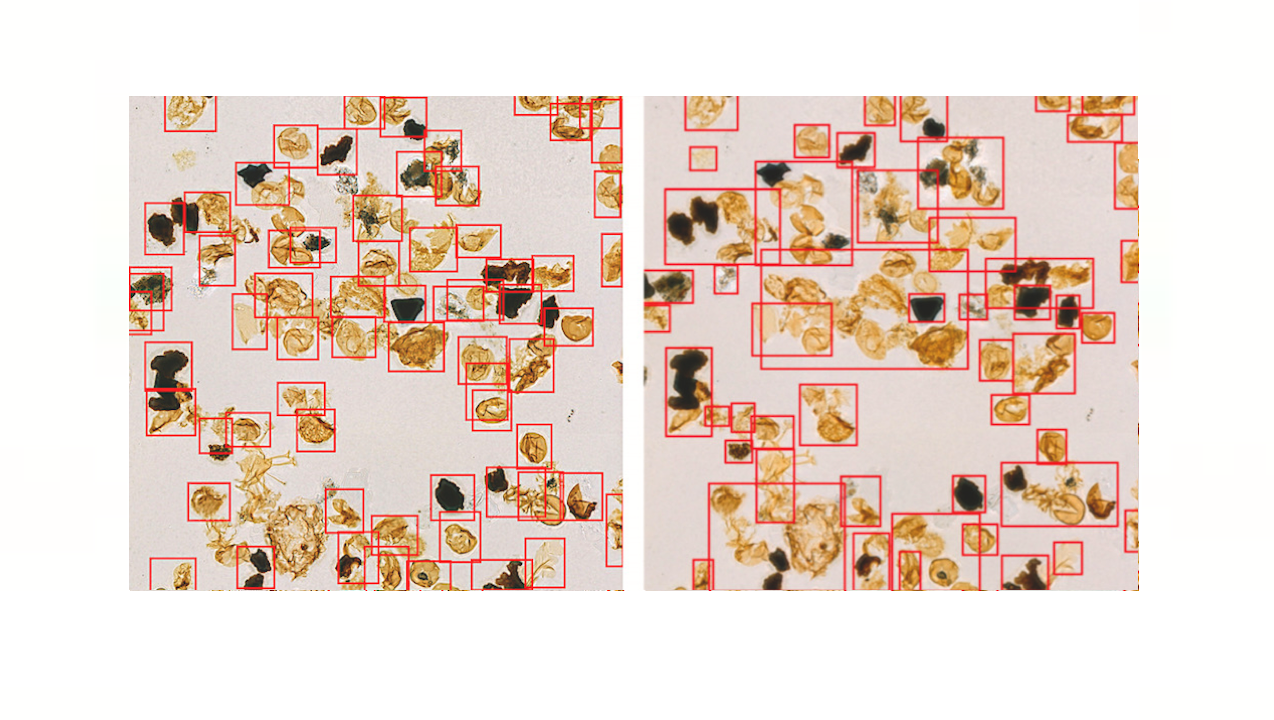
Protopia AI’s patented expertise allows Stained Glass Transforms™ to scale back the knowledge content material in inferencing information to extend information safety and allow privacy-preserving inference. The transforms could be regarded as a stained-glass overlaying the uncooked information behind the glass. Distinctly totally different from masking options, as an alternative of scanning the info to search out delicate data to redact, Protopia AI’s resolution stochastically transforms actual information with respect to the machine studying mannequin the info is meant for. The low-overhead and nonintrusive nature of Stained Glass Transforms™ allows enterprises to safe the possession of their information in more and more complicated environments by dynamically making use of the transformations in information pipelines for each file.
While artificial information could be helpful for coaching some fashions, inferencing requires actual information. On the opposite hand, inferencing on encrypted information is prohibitively gradual for many purposes even with customized {hardware}. By distinction, Protopia AI’s Stained Glass Transforms™ change the illustration of the info via a low-overhead software-only course of. These transforms are relevant and efficient for quite a lot of information sorts, together with however not restricted to tabular, textual content, picture, video, and many others. Protopia AI’s resolution allows decoupling the possession of information from the place and on which platform the inferencing is carried out.
Gartner has additionally lately highlighted Protopia AI in their June 2022 report on Cool Vendors in AI Governance and Responsible AI – From Principles to Practice.
Data sharing and defending information possession is a hindrance for utilizing SaaS for AI and machine studying. With Protopia AI, the particular goal machine studying mannequin remains to be capable of carry out correct inferencing with out the necessity to reverse the transformation. The goal mannequin remains to be skilled with the widespread practices and utilizing the unique information. As such, the answer seamlessly integrates with MLOps platforms and information shops. Ultimately, Protopia AI’s Stained-Glass Transforms decrease leakage of the delicate data entangled in inferencing information — which, in many circumstances, is the barrier to utilizing the info for machine studying and AI. “
Non Necessary cookies to view the content material.” data-cli-src=”https://player.vimeo.com/video/724475900?h=ebe8e0767c&dnt=1&app_id=122963″ width=”696″ peak=”392″ frameborder=”0″ permit=”autoplay; fullscreen; picture-in-picture” allowfullscreen>
In the sections that observe, we element how current strategies are complementary to Protopia AI’s Stained Glass Transform™ resolution and the place different options fall quick.
Federated Learning: To defend coaching information, Google introduced Federated Learning [1], a distributed studying framework in which the units on which information are domestically saved collaboratively be taught a shared ML mannequin with out the necessity to expose coaching information to a centralized coaching platform. The concept is to ship solely the ML fashions’ parameters to the cloud, thus defending the delicate coaching information. However, totally different works in the literature demonstrated that an attacker may use observations on an ML mannequin’s parameters to deduce personal data included in the coaching information, corresponding to class representatives, membership, and properties of a coaching information’s subset [2]. Moreover, Federated Learning ignores the inference stage of the ML lifecycle, and subsequently working inference nonetheless exposes the info to the ML mannequin whether or not it’s working on the cloud on the sting system.
Differential Privacy: There has been important consideration to the usage of Differential Privacy. This methodology gives margins on how a lot a single information file from the coaching dataset contributes to the machine studying mannequin. This is a membership take a look at on the coaching information information and it ensures if a single information file is faraway from the dataset, the output shouldn’t change past a sure threshold. Although essential, coaching in a differentially personal method nonetheless requires entry to plain-text information. More importantly, differential privateness doesn’t cope with the inferencing stage in any kind or means.
Synthetic Data: Another methodology to guard delicate coaching information is simply coaching the ML mannequin utilizing Synthetic Data. However, the generated artificial information won’t cowl attainable real-world information subspaces important to coach a predictive mannequin which might be dependable through the inference stage. This may trigger important accuracy losses that make the mannequin unusable after its deployment. Moreover, the skilled mannequin nonetheless wants to make use of actual information to carry out inferencing and prediction and there’s no escaping the challenges of this stage the place artificial information can’t be used.
Secure Multi-Party Computation and Homomorphic Encryption: Two cryptographic strategies for privacy-preserving computations are Secure Multi-Party Computation (SMC) and Homomorphic Encryption (HE). In SMC, the computation is distributed over a number of safe platforms that outcomes in important computation and communications prices which could be prohibitive in many circumstances [3]. Homomorphic encryption is much more pricey because it operates on the info in the encrypted trend that even with customized {hardware} is orders of magnitude slower [4]. Moreover, deep neural networks, which symbolize essentially the most used ML resolution in many domains these days, require some modifications for use in a framework that depends on HE [5].
Confidential Computing: Confidential computing focuses on defending information throughout use. Many huge firms like Google, Intel, Meta, and Microsoft have already joined the Confidential Computing Consortium, established in 2019 to advertise hardware-based Trusted Execution Environments (TEEs). This resolution goals at defending information whereas it’s being utilized by isolating computations to those hardware-based TEEs. The important disadvantage of Confidential Computing is that it forces firms to extend their prices emigrate their ML-based companies on platforms that present such specialised {hardware} infrastructures. At the identical time, this resolution can’t be thought of risk-free. Indeed, in May 2021, a gaggle of researchers launched SmashEx [6], an assault that enables accumulating and corrupting information from TEEs that depend on the Intel Software Guard Extension (SGX) expertise. Protopia AI’s Stained Glass Transform™ expertise can remodel information earlier than coming into the trusted execution setting and as such it’s complementary and minimizes the assault floor on an orthogonal axis. Even if the TEE is breached the plaintext information just isn’t there anymore with Protopia AI’s resolution.
In conclusion, enterprises have been struggling to know the right way to defend delicate data when utilizing their information throughout coaching and inference levels of the ML lifecycle. Questions of information possession and to whom, what platform, and what algorithms delicate information will get uncovered to throughout ML processes are a central problem to enabling ML options and unlocking their worth in right now’s enterprise. Protopia AI’s Stained Glass Transform™ resolution privatizes and protects ML information for each coaching and inference for any ML utility and information kind. These light-weight transformations decouple the possession of plain/uncooked delicate data in actual information from the ML course of with out imposing important overhead in the essential path nor requiring specialised {hardware}.
Note: Thanks to Protopia AI for the thought management/ Educational article above. Protopia AI has supported and sponsored this Content.
For extra data, merchandise, gross sales, and advertising, please contact Protopia AI workforce at [email protected]
References:
[1] McMahan, Brendan, et al. “Communication-efficient studying of deep networks from decentralized information.” Artificial intelligence and statistics. PMLR, 2017.
[2] Lyu, Lingjuan, et al. “Privacy and robustness in federated studying: Attacks and defenses.” arXiv preprint arXiv:2012.06337 (2020).
[3] Mohassel, Payman, and Yupeng Zhang. “Secureml: A system for scalable privacy-preserving machine studying.” 2017 IEEE symposium on safety and privateness (SP). IEEE, 2017.
[4] Xie, Pengtao, et al. “Crypto-nets: Neural networks over encrypted information.” arXiv preprint arXiv:1412.6181 (2014).
[5] Chabanne, Hervé, et al. “Privacy-preserving classification on deep neural community.” Cryptology ePrint Archive (2017).
[6] Cui, Jinhua, et al. “SmashEx: Smashing SGX Enclaves Using Exceptions.” Proceedings of the 2021 ACM SIGSAC Conference on Computer and Communications Security. 2021.
Luca is Ph.D. pupil on the Department of Computer Science of the University of Milan. His pursuits are Machine Learning, Data Analysis, IoT, Mobile Programming, and Indoor Positioning. His analysis at the moment focuses on Pervasive Computing, Context-awareness, Explainable AI, and Human Activity Recognition in sensible environments.
https://www.marktechpost.com/2022/09/08/3-machine-learning-business-challenges-rooted-in-data-sensitivity/