We are excited to convey Transform 2022 again in-person July 19 and nearly July 20 – August 3. Join AI and knowledge leaders for insightful talks and thrilling networking alternatives. Learn extra about Transform 2022
AI is a quickly rising expertise that has many advantages for society. However, as with all new applied sciences, misuse is a possible danger. One of the most troubling potential misuses of AI could be present in the type of adversarial AI assaults.
In an adversarial AI assault, AI is used to control or deceive one other AI system maliciously. Most AI applications be taught, adapt and evolve by behavioral studying. This leaves them susceptible to exploitation as a result of it creates house for anybody to show an AI algorithm malicious actions, finally resulting in adversarial outcomes. Cybercriminals and risk actors can exploit this vulnerability for malicious functions and intent.
Although most adversarial assaults have to date been carried out by researchers and inside labs, they’re a rising matter of concern. The prevalence of an adversarial assault on AI or a machine studying algorithm highlights a deep crack in the AI mechanism. The presence of such vulnerabilities inside AI methods can stunt AI progress and improvement and develop into a major safety danger for folks utilizing AI-integrated methods. Therefore, to completely make the most of the potential of AI methods and algorithms, it’s essential to know and mitigate adversarial AI assaults.
Understanding adversarial AI assaults
Although the fashionable world we stay in now could be deeply layered with AI, it has but to take over the world totally. Since its creation, AI has been met with moral criticisms, which has sparked a standard hesitation in totally adopting it. However, the rising concern that the vulnerabilities in machine studying fashions and AI algorithms can develop into a component of malicious functions is an enormous hindrance in AI/ML progress.
The primary parallels of an adversarial assault are basically the similar: manipulating an AI algorithm or an ML mannequin to provide malicious outcomes. However, an adversarial assault usually entails the two following issues:
Poisoning: the ML mannequin is fed with inaccurate or misinterpreted knowledge to dupe it into making an faulty prediction Contaminating: the ML mannequin is fed with maliciously designed knowledge to deceive an already skilled mannequin into conducting malicious actions and predictions. In each strategies, contamination is most probably to develop into a widespread downside. Since the method includes a malicious actor injecting or feeding unfavourable info, these actions can rapidly develop into a widespread downside with the assist of different assaults. In distinction, it appears simple to manage and forestall poisoning since offering a coaching dataset would necessitate an insider job. It is feasible to forestall such insider threats with a zero-trust safety mannequin and different community safety protocols.
However, defending a enterprise in opposition to adversarial threats will probably be a tough activity. While typical on-line safety points are simple to mitigate utilizing numerous instruments equivalent to residential proxies, VPNs, and even antimalware software program, adversarial AI threats would possibly overcome these vulnerabilities, rendering these instruments too primitive to allow safety.
How is adversarial AI a risk?
AI is already a well-integrated, key half of important fields equivalent to finance, healthcare and transportation. Security points in these fields could be significantly hazardous to all human lives. Since AI is properly built-in inside human lives, the impression of adversarial threats in AI can wreak large havoc.
In 2018, an Office of the Director of National Security report highlighted a number of Adversarial Machine studying threats. Amidst the threats listed in the report, one of the most urgent considerations was the potential that these assaults had in compromising pc imaginative and prescient algorithms.
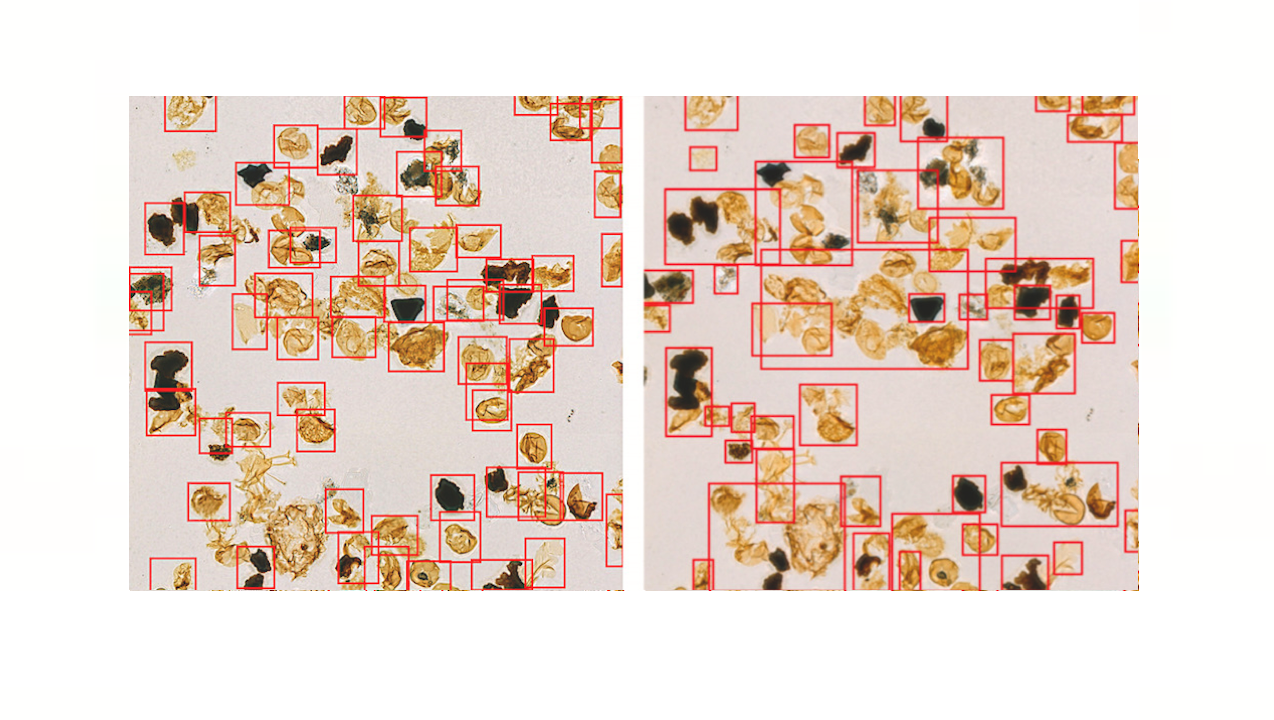
Research has to date come throughout a number of examples of AI positioning. One such examine concerned researchers including small adjustments or “perturbations” to a picture of a panda, invisible to the bare eye. The adjustments prompted the ML algorithm to determine the picture of the panda as that of a gibbon.
Similarly, one other examine highlights the chance of AI contamination which concerned attackers duping the facial recognition cameras with infrared gentle. This motion allowed these assaults to mitigate correct recognition and will allow them to impersonate different folks.
Moreover, adversarial assaults are additionally evident in e-mail spam filter manipulation. Since e-mail spam filter instruments efficiently filter spam emails by monitoring sure phrases, attackers can manipulate these instruments through the use of acceptable phrases and phrases, having access to the recipient’s inbox. Therefore, whereas contemplating these examples and researches, it’s simple to determine the impression of adversarial AI assaults on the cyber risk panorama, equivalent to:
Adversarial AI opens the chance of rendering AI-based safety instruments equivalent to phishing filters ineffective. IoT units are AI-based. Adversarial assaults on them might result in large-scale hacking makes an attempt. AI instruments have a tendency to gather private info. Attacks can manipulate these instruments to disclose collected private info. AI is a component of the protection system. Adversarial assaults on protection instruments can put nationwide safety in peril. It can convey a couple of new selection of assaults that stay undetected. It is ever extra essential to take care of safety and vigilance in opposition to adversarial AI assaults.
Is there any prevention?
Considering the potential AI improvement has in making human lives extra manageable and way more refined, researchers are already devising numerous methods for shielding methods in opposition to adversarial AI. One such technique is adversarial coaching, which includes pre-training the machine studying algorithm in opposition to positioning and contamination makes an attempt by feeding it with potential perturbations.
In the case of pc imaginative and prescient algorithms, the algorithms will come pre-disposed with photos and their altercations. For instance, a automobile visible algorithm designed to determine the cease signal could have discovered all the potential alterations of the cease signal, equivalent to with stickers, graffiti, and even lacking letters. The algorithm will appropriately determine the phenomena regardless of the attacker’s manipulations. However, this technique will not be foolproof since it’s not possible to determine all potential adversarial assault iterations.
The algorithm employs non-intrusive picture high quality options to tell apart between respectable and adversarial inputs. The method can probably be certain that adversarial machine studying importer and alternation are neutralized earlier than reaching the classification info. Another such technique contains pre-processing and denoising, which routinely removes potential adversarial noise from the enter.
Conclusion
Despite its prevalent use in the fashionable world, AI has but to take over. Although machine studying and AI have managed to develop and even dominate some areas of our each day lives, they continue to be considerably below improvement. Until researchers can totally acknowledge the potential of AI and machine studying, there’ll stay a gaping gap in the best way to mitigate adversarial threats inside AI expertise. However, analysis on the matter remains to be ongoing, primarily as a result of it’s important to AI improvement and adoption.
Waqas is a cybersecurity journalist and author.
DataDecisionMakers
Welcome to the VentureBeat neighborhood!
DataDecisionMakers is the place consultants, together with the technical folks doing knowledge work, can share data-related insights and innovation.
If you wish to examine cutting-edge concepts and up-to-date info, finest practices, and the future of knowledge and knowledge tech, be part of us at DataDecisionMakers.
You would possibly even contemplate contributing an article of your personal!
Read More From DataDecisionMakers
https://venturebeat.com/2022/04/03/adversarial-ai-and-the-dystopian-future-of-tech/