Machine studying could be utilized in numerous methods in safety, for occasion, in malware evaluation, to make predictions, and for clustering safety occasions. It may also be used to detect beforehand unknown assaults with no established signature.
Wendy Edwards, a software program developer within the intersection of cybersecurity and information science, spoke about making use of machine studying to safety at The Diana Initiative 2021.
Artificial Intelligence (AI) could be utilized to detect anomalies by discovering uncommon patterns. But uncommon doesn’t essentially imply malicious, as Edwards defined:
For instance, possibly your net server is experiencing greater than normal site visitors as a result of one thing is trending on social media. You could possibly study issues associated to the site visitors to make that call. For instance, are there plenty of HTTP requests with the “User-agent” set to one thing not usually related to regular net searching? Is there a variety of unexplained site visitors originating from a single IP or IP vary? An uncommon sequence of accesses to endpoints may counsel fuzzing.
With AI and machine studying, there are methods to cope with plenty of enter variables and set up a conclusion. Edwards gave an instance of how forecasting means that you can use time sequence information to make predictions concerning the future, and helps traits, seasons, and cycles:
This could possibly be helpful for measuring CPU utilization or complete net server entry. It’s fairly attainable {that a} system will usually be busiest throughout sure instances of the day. Perhaps the hits on a brand new web site are regularly trending up. Statistical metrics may also be helpful, e.g. imply and commonplace deviation. This can assist us decide what an “uncommon” quantity of exercise from a single IP or IP vary truly is.
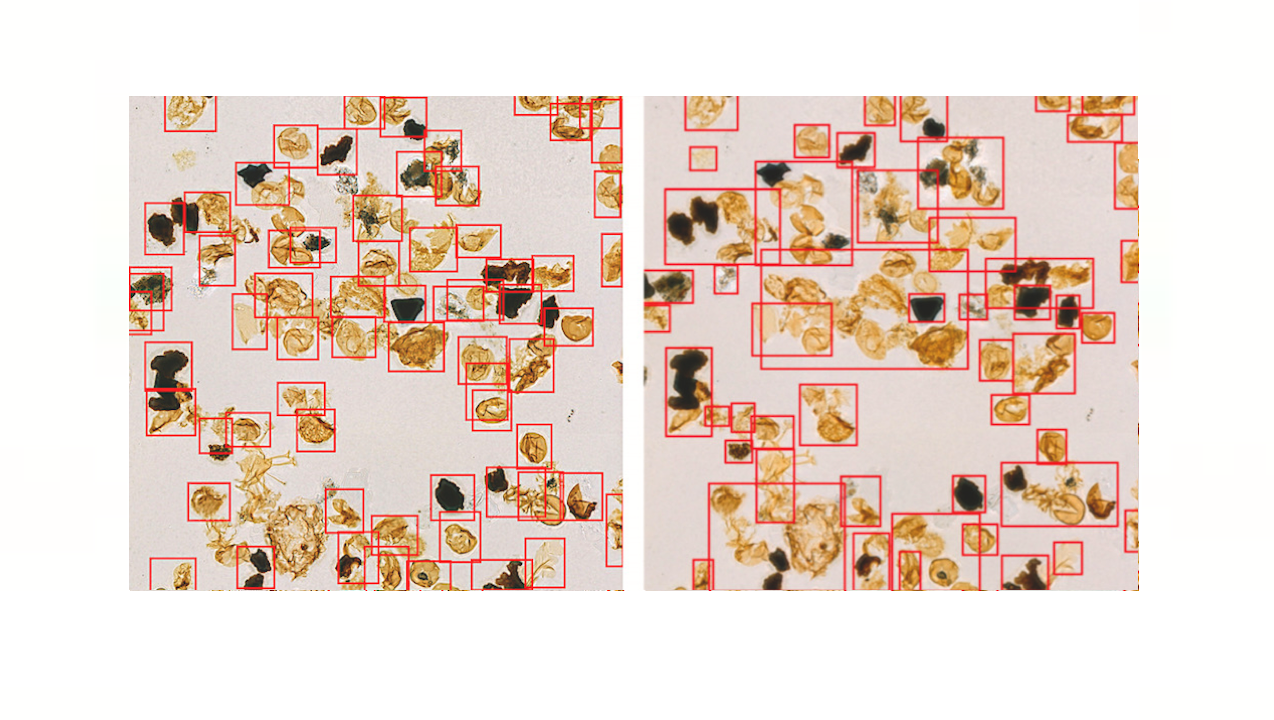
Edwards confirmed how machine studying can be utilized to cluster safety occasions:
Clustering is a machine studying method to create teams of knowledge factors which might be extra comparable to one another than outdoors factors. Security incidents are units of occasions, and infrequently the identical set of occasions with the identical root trigger present up in a number of places.
For instance, a Trojan Horse may assault plenty of machines, however the root trigger and remediation could be the identical.
Clustering helps Security Operation Center (SOC) analysts determine comparable incidents, which might typically require the identical response. This can save time by eliminating a variety of tedious work, Edwards talked about.
InfoQ interviewed Wendy Edwards about how machine studying is being utilized in safety.
InfoQ: What’s the state of follow on making use of synthetic intelligence in IT safety?
Wendy Edwards: It’s steadily bettering, although I believe there’ll at all times be a necessity for expert practitioners; synthetic intelligence and machine studying is unlikely to exchange folks. Artificial intelligence has grown considerably over the previous 15 years, and cybersecurity has additionally develop into much more difficult due to larger complexity in computing.
At this level, there’s been in depth analysis and growth associated to potential functions of synthetic intelligence in cybersecurity, together with intrusion detection, malware evaluation, phishing detection, and discovering bot accounts on social media. Natural language processing has performed a job as nicely, most clearly in spam detection, but additionally in figuring out malicious code in obfuscated scripts.
Just take a look at the variety of distributors telling you about how their merchandise use machine studying! However, there’s not a broadly accepted set of finest practices about AI and cybersecurity at this level.
InfoQ: You talked about in your speak that anomaly-based detection has the potential to detect beforehand unknown assaults with no established signature. How does this work?
Edwards: This pertains to the query about establishing what’s regular and what’s malicious. A signature is a algorithm associated to a identified assault, so there wouldn’t be any for an assault that hadn’t been seen earlier than.
When we see one thing anomalous with no benign rationalization, one thing could also be improper. For instance, if one thing in your web site is trending on social media, you may even see elevated exercise and that’s OK. But in case you’re seeing a variety of exercise that doesn’t correspond with regular consumer conduct, chances are you’ll be underneath assault.
InfoQ: What AI instruments can be found and the way can we use them?
Edwards: There are plenty of established freely out there instruments; for instance, Python has scikit-learn. Google and Facebook have launched the Tensorflow and PyTorch libraries respectively.
Scikit-learn provides a variety of helpful instruments, together with regression, clustering, classification, and extra.
Tensorflow and PyTorch help extra complicated duties, like deep studying. Generally, PyTorch is taken into account simpler for skilled Python programmers to make use of, and TensorFlow is taken into account extra prepared for use in a manufacturing setting.
InfoQ: What do you anticipate the longer term will convey on the subject of AI and IT safety?
Edwards: I believe adversaries can even leverage synthetic intelligence in assaults. The Internet of Things (IoT) and different rising applied sciences will create an more and more giant assault floor, and attackers might leverage AI to search out methods to take advantage of this. According to a National Academy of Science report Implications of Artificial Intelligence for Cybersecurity, using AI and ML for discovering and weaponizing new vulnerabilities is within the conceptualization and growth stage within the United States, and certain in China and Israel as nicely.
Adversarial machine studying refers to makes an attempt to idiot machine studying algorithms. For instance, a spammer might try and evade filtering by misspelling “dangerous” phrases and together with “good” phrases not generally related to filters. If operational information is used to coach future techniques, an attacker might try and contaminate this information.
One instance of that is the Microsoft “Tay” bot. After being bombarded by racist and sexist messages from trolls, Tay started to tweet offensive issues and ended up being shut down after about 16 hours.