The Transform Technology Summits begin October thirteenth with Low-Code/No Code: Enabling Enterprise Agility. Register now!
Machine learning has turn out to be an vital part of many purposes we use at present. And including machine learning capabilities to purposes is changing into more and more simple. Many ML libraries and on-line providers don’t even require a radical information of machine learning.
However, even easy-to-use machine learning techniques include their very own challenges. Among them is the specter of adversarial assaults, which has turn out to be one of many vital considerations of ML purposes.
Adversarial assaults are completely different from different sorts of security threats that programmers are used to coping with. Therefore, step one to countering them is to perceive the several types of adversarial assaults and the weak spots of the machine learning pipeline.
In this publish, I’ll attempt to present a zoomed-out view of the adversarial assault and protection panorama with assist from a video by Pin-Yu Chen, AI researcher at IBM. Hopefully, this can assist programmers and product managers who don’t have a technical background in machine learning get a greater grasp of how they’ll spot threats and shield their ML-powered purposes.
1- Know the distinction between software program bugs and adversarial assaults
Software bugs are well-known amongst builders, and we have now loads of instruments to discover and repair them. Static and dynamic evaluation instruments discover security bugs. Compilers can discover and flag deprecated and doubtlessly dangerous code use. Test models can make sure that features reply to completely different sorts of enter. Anti-malware and different endpoint options can discover and block malicious applications and scripts within the browser and the pc arduous drive. Web utility firewalls can scan and block dangerous requests to net servers, similar to SQL injection instructions and a few sorts of DDoS assaults. Code and app internet hosting platforms similar to GitHub, Google Play, and Apple App Store have loads of behind-the-scenes processes and instruments that vet purposes for security.
In a nutshell, though imperfect, the normal cybersecurity panorama has matured to cope with completely different threats.
But the character of assaults in opposition to machine learning and deep learning techniques is completely different from different cyber threats. Adversarial assaults financial institution on the complexity of deep neural networks and their statistical nature to discover methods to exploit them and modify their conduct. You can’t detect adversarial vulnerabilities with the basic instruments used to harden software program in opposition to cyber threats.
In current years, adversarial examples have caught the eye of tech and enterprise reporters. You’ve in all probability seen a number of the many articles that present how machine learning fashions mislabel photographs which have been manipulated in methods which can be imperceptible to the human eye.
Above: Adversarial assaults manipulate the conduct of machine learning fashions (credit score: Pin-Yu Chen)While most examples present assaults in opposition to picture classification machine learning techniques, different sorts of media will also be manipulated with adversarial examples, together with textual content and audio.
“It is a type of common threat and concern once we are speaking about deep learning expertise normally,” Chen says.
One false impression about adversarial assaults is that it impacts ML fashions that carry out poorly on their most important duties. But experiments by Chen and his colleagues present that, normally, fashions that carry out their duties extra precisely are much less sturdy in opposition to adversarial assaults.
“One pattern we observe is that extra correct fashions appear to be extra delicate to adversarial perturbations, and that creates an undesirable tradeoff between accuracy and robustness,” he says.
Ideally, we wish our fashions to be each correct and sturdy in opposition to adversarial assaults.
Above: Experiments present that adversarial robustness drops because the ML mannequin’s accuracy grows (credit score: Pin-Yu Chen)2- Know the affect of adversarial assaults
In adversarial assaults, context issues. With deep learning able to performing sophisticated duties in laptop imaginative and prescient and different fields, they’re slowly discovering their manner into delicate domains similar to healthcare, finance, and autonomous driving.
But adversarial assaults present that the decision-making strategy of deep learning and people are basically completely different. In safety-critical domains, adversarial assaults may cause threat to the life and well being of the individuals who can be straight or not directly utilizing the machine learning fashions. In areas like finance and recruitment, it will probably deprive folks of their rights and trigger reputational injury to the corporate that runs the fashions. In security techniques, attackers can sport the fashions to bypass facial recognition and different ML-based authentication techniques.
Overall, adversarial assaults trigger a belief drawback with machine learning algorithms, particularly deep neural networks. Many organizations are reluctant to use them due to the unpredictable nature of the errors and assaults that may occur.
If you’re planning to use any type of machine learning, take into consideration the affect that adversarial assaults can have on the perform and selections that your utility makes. In some circumstances, utilizing a lower-performing however predictable ML mannequin could be higher than one that may be manipulated by adversarial assaults.
3- Know the threats to ML fashions
The time period adversarial assault is commonly used loosely to refer to several types of malicious exercise in opposition to machine learning fashions. But adversarial assaults differ primarily based on what a part of the machine learning pipeline they aim and the type of exercise they contain.
Basically, we are able to divide the machine learning pipeline into the “coaching section” and “check section.” During the coaching section, the ML staff gathers information, selects an ML structure, and trains a mannequin. In the check section, the skilled mannequin is evaluated on examples it hasn’t seen earlier than. If it performs on par with the specified standards, then it’s deployed for manufacturing.
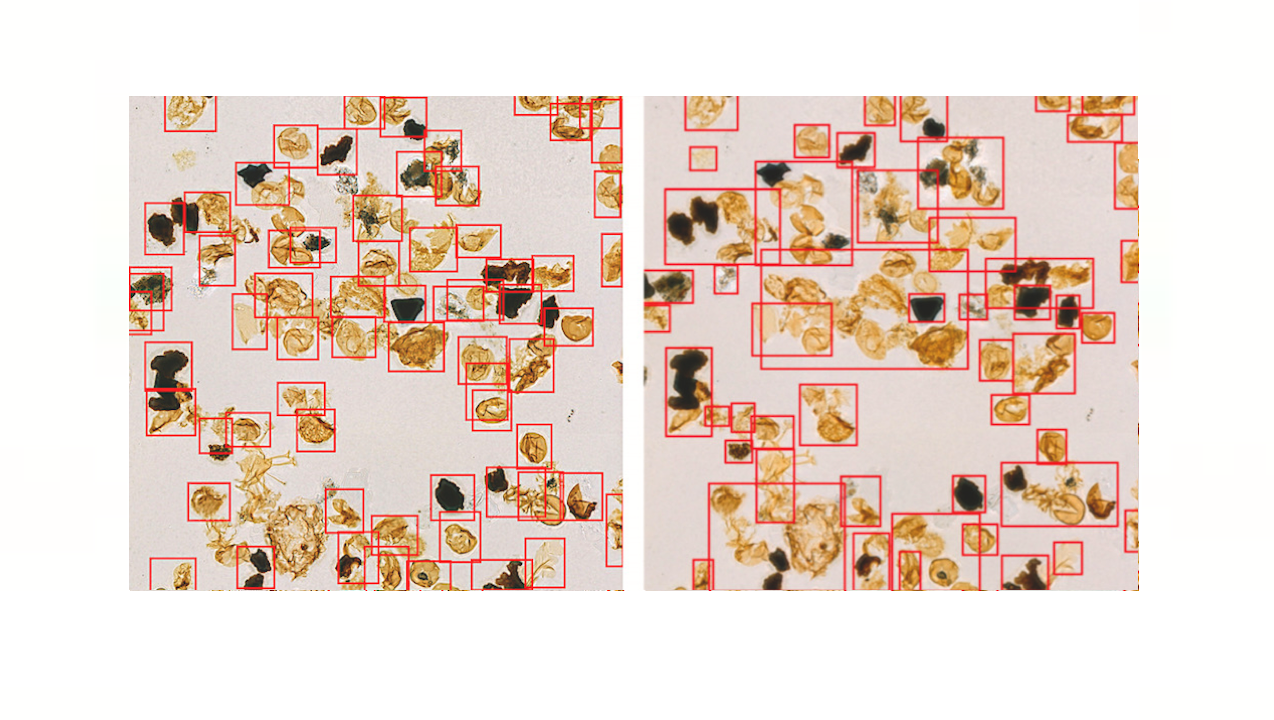
Above: The machine learning pipeline (credit score: Pin-Yu Chen)The machine learning pipeline (credit score: Pin-Yu Chen)Adversarial assaults which can be distinctive to the coaching section embody information poisoning and backdoors. In information poisoning assaults, the attacker inserts manipulated information into the coaching dataset. During coaching, the mannequin tunes its parameters on the poisoned information and turns into delicate to the adversarial perturbations they include. A poisoned mannequin may have erratic conduct at inference time. Backdoor assaults are a particular kind of knowledge poisoning, during which the adversary implants visible patterns within the coaching information. After coaching, the attacker makes use of these patterns throughout inference time to set off particular conduct within the goal ML mannequin.
Test section or “inference time” assaults are the sorts of assaults that focus on the mannequin after coaching. The hottest kind is “mannequin evasion,” which is mainly the everyday adversarial examples which have turn out to be common. An attacker creates an adversarial instance by beginning with a standard enter (e.g., a picture) and progressively including noise to it to skew the goal mannequin’s output towards the specified end result (e.g., a particular output class or normal lack of confidence).
Another class of inference-time assaults tries to extract delicate info from the goal mannequin. For instance, membership inference assaults use completely different strategies to trick the goal ML mannequin to reveal its coaching information. If the coaching information included delicate info similar to bank card numbers or passwords, these kind of assaults could be very damaging.
Above: Different sorts of adversarial assaults (credit score: Pin-Yu Chen)Another vital think about machine learning security is mannequin visibility. When you utilize a machine learning mannequin that’s printed on-line, say on GitHub, you’re utilizing a “white field” mannequin. Everyone else can see the mannequin’s structure and parameters, together with attackers. Having direct entry to the mannequin will make it simpler for the attacker to create adversarial examples.
When your machine learning mannequin is accessed by an internet API similar to Amazon Recognition, Google Cloud Vision, or another server, you’re utilizing a “black field” mannequin. Black-box ML is more durable to assault as a result of the attacker solely has entry to the output of the mannequin. But more durable doesn’t imply unattainable. It is price noting there are a number of model-agnostic adversarial assaults that apply to black-box ML fashions.
4- Know what to search for
What does this all imply for you as a developer or product supervisor? “Adversarial robustness for machine learning actually differentiates itself from conventional security issues,” Chen says.
The security group is progressively growing instruments to construct extra sturdy ML fashions. But there’s nonetheless a number of work to be accomplished. And for the second, your due diligence can be an important think about defending your ML-powered purposes in opposition to adversarial assaults.
Here are a number of questions it is best to ask when contemplating utilizing machine learning fashions in your purposes:
Where does the coaching information come from? Images, audio, and textual content information might sound innocuous per se. But they’ll disguise malicious patterns that may poison the deep learning mannequin that can be skilled by them. If you’re utilizing a public dataset, make sure that the info comes from a dependable supply, probably vetted by a identified firm or an instructional establishment. Datasets which have been referenced and utilized in a number of analysis initiatives and utilized machine learning applications have greater integrity than datasets with unknown histories.
What type of information are you coaching your mannequin on? If you’re utilizing your individual information to prepare your machine learning mannequin, does it embody delicate info? Even in the event you’re not making the coaching information public, membership inference assaults would possibly allow attackers to uncover your mannequin’s secrets and techniques. Therefore, even in the event you’re the only proprietor of the coaching information, it is best to take further measures to anonymize the coaching information and shield the data in opposition to potential assaults on the mannequin.
Who is the mannequin’s developer? The distinction between a innocent deep learning mannequin and a malicious one will not be within the supply code however within the thousands and thousands of numerical parameters they comprise. Therefore, conventional security instruments can’t let you know whether or not if a mannequin has been poisoned or whether it is susceptible to adversarial assaults. So, don’t simply obtain some random ML mannequin from GitHub or PyTorch Hub and combine it into your utility. Check the integrity of the mannequin’s writer. For occasion, if it comes from a famend analysis lab or an organization that has pores and skin within the sport, then there’s little likelihood that the mannequin has been deliberately poisoned or adversarially compromised (although the mannequin would possibly nonetheless have unintentional adversarial vulnerabilities).
Who else has entry to the mannequin? If you’re utilizing an open-source and publicly out there ML mannequin in your utility, then you have to assume that potential attackers have entry to the identical mannequin. They can deploy it on their very own machine and check it for adversarial vulnerabilities, and launch adversarial assaults on another utility that makes use of the identical mannequin out of the field. Even in the event you’re utilizing a business API, you have to take into account that attackers can use the very same API to develop an adversarial mannequin (although the prices are greater than white-box fashions). You should set your defenses to account for such malicious conduct. Sometimes, including easy measures similar to operating enter photographs by a number of scaling and encoding steps can have an incredible affect on neutralizing potential adversarial perturbations.
Who has entry to your pipeline? If you’re deploying your individual server to run machine learning inferences, take nice care to shield your pipeline. Make certain your coaching information and mannequin backend are solely accessible by people who find themselves concerned within the growth course of. If you’re utilizing coaching information from exterior sources (e.g., user-provided photographs, feedback, opinions, and so on.), set up processes to stop malicious information from coming into the coaching/deployment course of. Just as you sanitize consumer information in net purposes, you must also sanitize information that goes into the retraining of your mannequin. As I’ve talked about earlier than, detecting adversarial tampering on information and mannequin parameters could be very tough. Therefore, you have to make sure that to detect modifications to your information and mannequin. If you’re frequently updating and retraining your fashions, use a versioning system to roll again the mannequin to a earlier state in the event you discover out that it has been compromised.
5- Know the instruments
Above: The Adversarial ML Threat Matrix to present weak spots within the machine learning pipelineAdversarial assaults have turn out to be an vital space of focus within the ML group. Researchers from academia and tech corporations are coming collectively to develop instruments to shield ML fashions in opposition to adversarial assaults.Earlier this yr, AI researchers at 13 organizations, together with Microsoft, IBM, Nvidia, and MITRE, collectively printed the Adversarial ML Threat Matrix, a framework meant to assist builders detect potential factors of compromise within the machine learning pipeline. The ML Threat Matrix is vital as a result of it doesn’t solely deal with the security of the machine learning mannequin however on all of the elements that comprise your system, together with servers, sensors, web sites, and so on.
The AI Incident Database is a crowdsourced financial institution of occasions during which machine learning techniques have gone incorrect. It can assist you study in regards to the potential methods your system would possibly fail or be exploited.
Big tech corporations have additionally launched instruments to harden machine learning fashions in opposition to adversarial assaults. IBM’s Adversarial Robustness Toolbox is an open-source Python library that gives a set of features to consider ML fashions in opposition to several types of assaults. Microsoft’s Counterfit is one other open-source software that checks machine learning fashions for adversarial vulnerabilities.
Machine learning wants new views on security. We should study to regulate our software program growth practices in accordance to the rising threats of deep learning because it turns into an more and more vital a part of our purposes. Hopefully, the following pointers will show you how to higher perceive the security concerns of machine learning.
Ben Dickson is a software program engineer and the founding father of TechTalks. He writes about expertise, enterprise, and politics.VentureBeat
VentureBeat’s mission is to be a digital city sq. for technical decision-makers to acquire information about transformative expertise and transact.
Our web site delivers important info on information applied sciences and techniques to guide you as you lead your organizations. We invite you to turn out to be a member of our group, to entry:
up-to-date info on the topics of curiosity to you
our newsletters
gated thought-leader content material and discounted entry to our prized occasions, similar to Transform 2021: Learn More
networking options, and extra
Become a member